How to Require MFA for All Users with Conditional Access: A Zero Trust Guide
In today's complex digital landscape, the traditional security model of a fortified corporate network is no longer sufficient. With the rise of remote work, cloud services, and sophisticated cyber threats, a new paradigm is essential: Zero Trust. This modern security strategy operates on a simple but powerful principle: "Never trust, always verify." It assumes that a breach is inevitable and treats every access request as if it originated from an open network. At the heart of this model is the verification of identity, and the most critical first step in securing identity is implementing Multi-Factor Authentication (MFA).
As Alex Weinert, Microsoft's Director of Identity Security, famously stated: "Your password doesn't matter, but MFA does! Based on our studies, your account is more than 99.9% less likely to be compromised if you use MFA." [1]
This article provides a practical, step-by-step guide for IT administrators to implement a foundational Zero Trust policy: requiring MFA for all users. We will use Microsoft Entra Conditional Access, the powerful policy engine at the core of Microsoft's Zero Trust framework, to build and deploy this essential security control. By the end of this guide, you will have a robust, testable, and compliant MFA policy protecting your entire organization.
What is Conditional Access?
Conditional Access is Microsoft's Zero Trust policy engine that brings signals together to make decisions and enforce organizational policies. Think of it as an intelligent bouncer for your digital resources. It evaluates every access attempt based on various signals—such as the user, their location, the device they're using, and the application they're trying to access—and then decides whether to grant access, block it, or require additional verification steps, like MFA.
🔑 Key Concept: Conditional Access moves security from a static, network-based perimeter to a dynamic, identity-based one. It's not about where you are, but who you are and how you are accessing resources.
Components of a Conditional Access Policy
To build an effective policy, you need to understand its core components. Each policy is an "if-then" statement: if an assignment is met, then apply the access controls.
| Component | Description | Example |
|---|---|---|
| Assignments (If) | Defines the scope of the policy: who it applies to (Users), what they are accessing (Target resources), and under what context (Conditions like location, device, risk). | "All users" accessing "All cloud apps" from an "untrusted location". |
| Access Controls (Then) | Specifies the action to be taken. This can be to grant access (with requirements like MFA) or to block access. | "Grant access" but "Require multifactor authentication". |
Step-by-Step Guide: Requiring MFA for All Users
Let's walk through creating the most fundamental and impactful Conditional Access policy: requiring MFA for every user accessing any cloud application.
📋 Prerequisites
Before you begin, ensure you have:
- License: Microsoft Entra ID P1 or P2.
- Permissions: Conditional Access Administrator or Security Administrator role.
- Emergency Accounts: At least two "break-glass" accounts that are excluded from the policy to prevent lockout.
- Test User: A non-administrator test user to validate the policy.
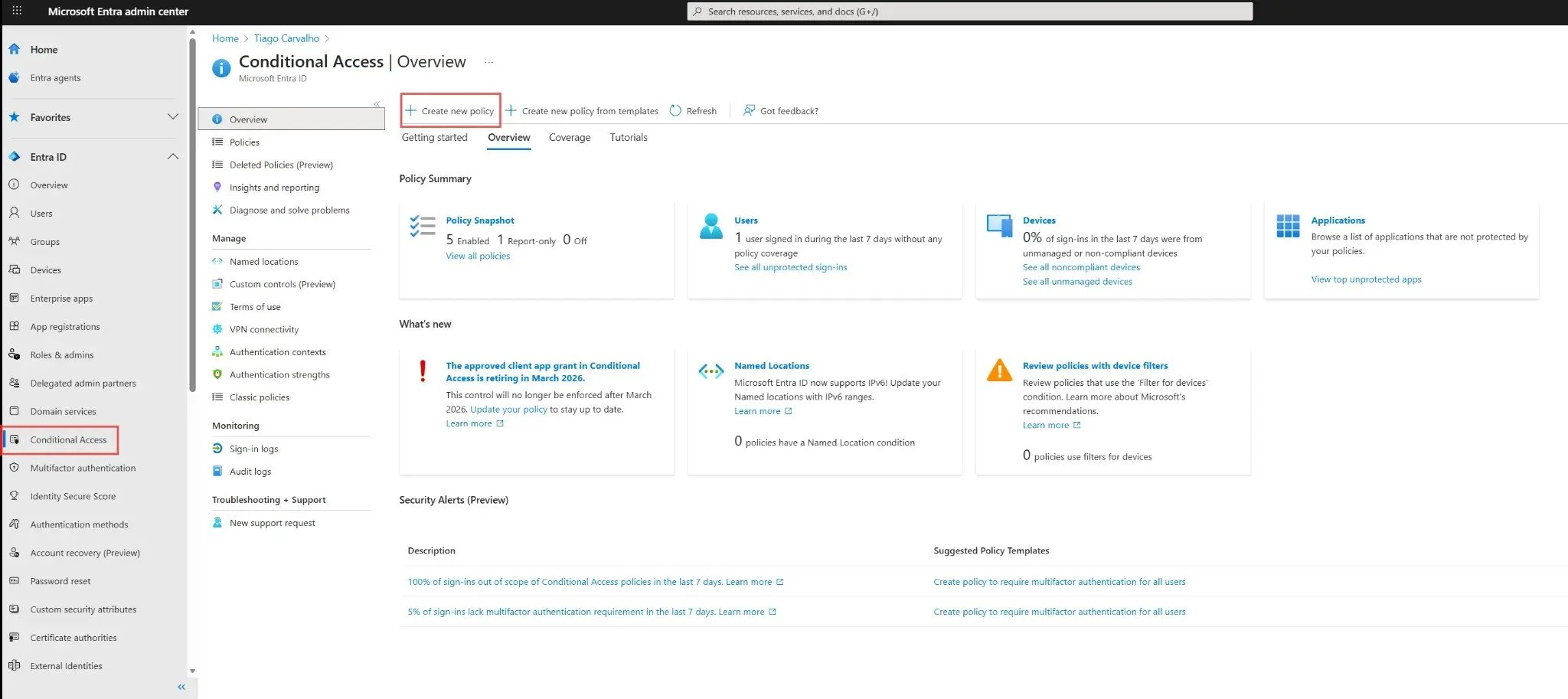
Step 1: Navigate to Conditional Access
Sign in to the Microsoft Entra admin center. In the left navigation menu, go to Protection > Conditional Access. This is the central hub for all your policies.
Figure 1: The Conditional Access overview page in the Microsoft Entra admin center.
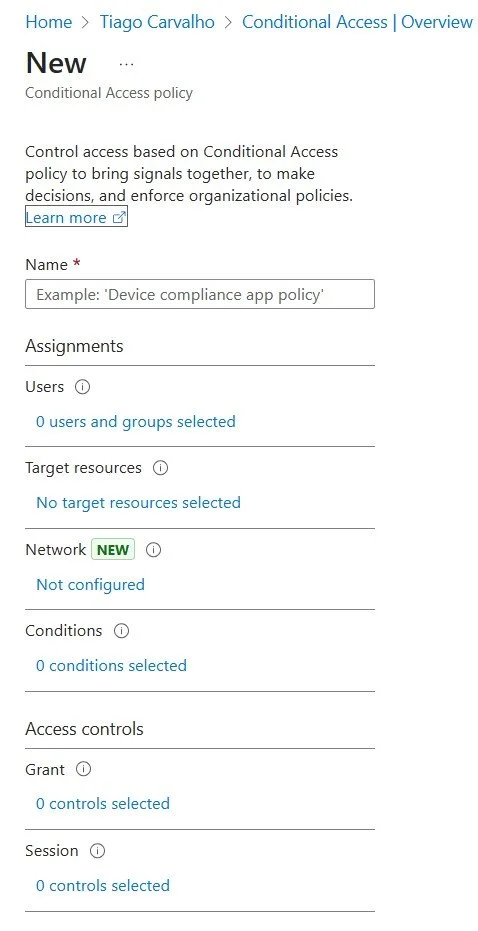
Step 2: Create a New Policy
Click on + Create new policy. This will open the configuration blade for a new policy. Give your policy a descriptive name, such as "MFA for All Users".
Figure 2: The initial blade for creating a new Conditional Access policy.
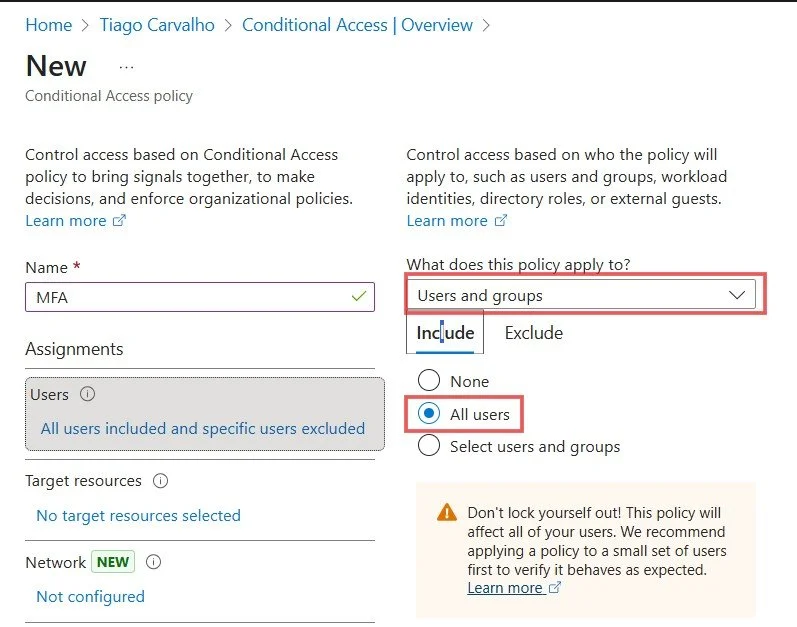
Step 3: Configure Assignments - Users
Under Assignments, click on Users. Select All users under the "Include" tab. It is critical to exclude your emergency access accounts to prevent being locked out.
- Under the Exclude tab, select Users and groups.
- Check the box for your emergency access accounts.
⚠️ Important: Always exclude at least two emergency access accounts from your MFA policies. This is your safety net if a policy misconfiguration locks out other administrators.
Figure 3: Including all users and excluding emergency access accounts.
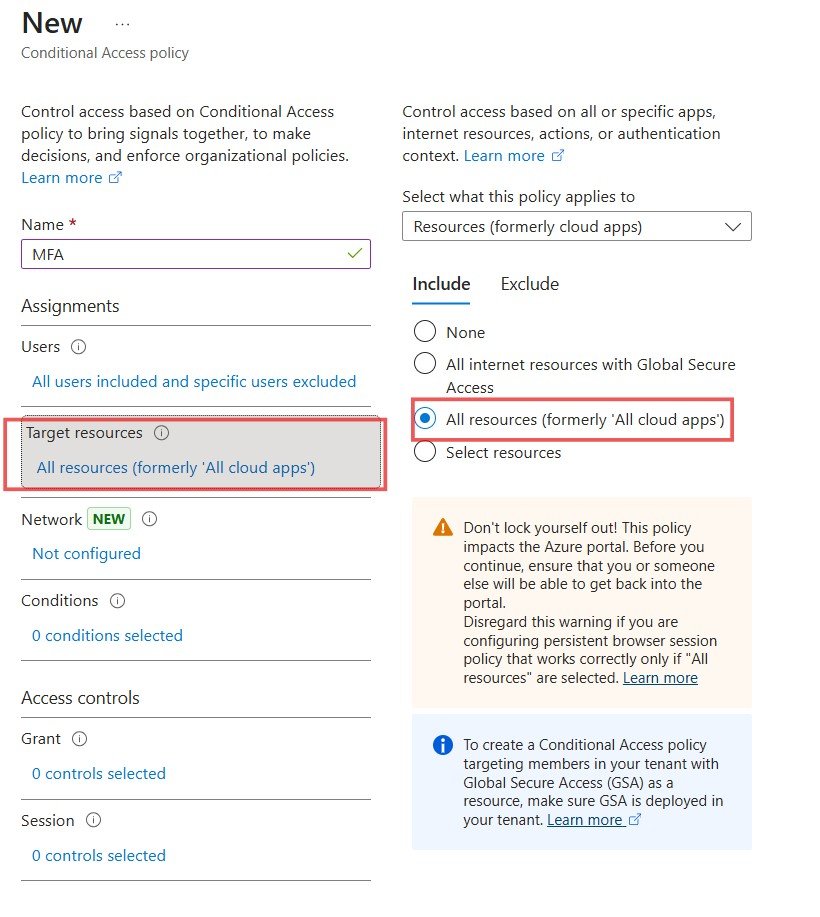
Step 4: Configure Assignments - Target Resources
Next, click on Target resources. To apply this policy broadly for maximum security, select All cloud apps under the "Include" tab. This ensures that any sign-in to any application integrated with Microsoft Entra ID will be protected by MFA.
Figure 4: Selecting 'All cloud apps' to enforce the policy across all applications.
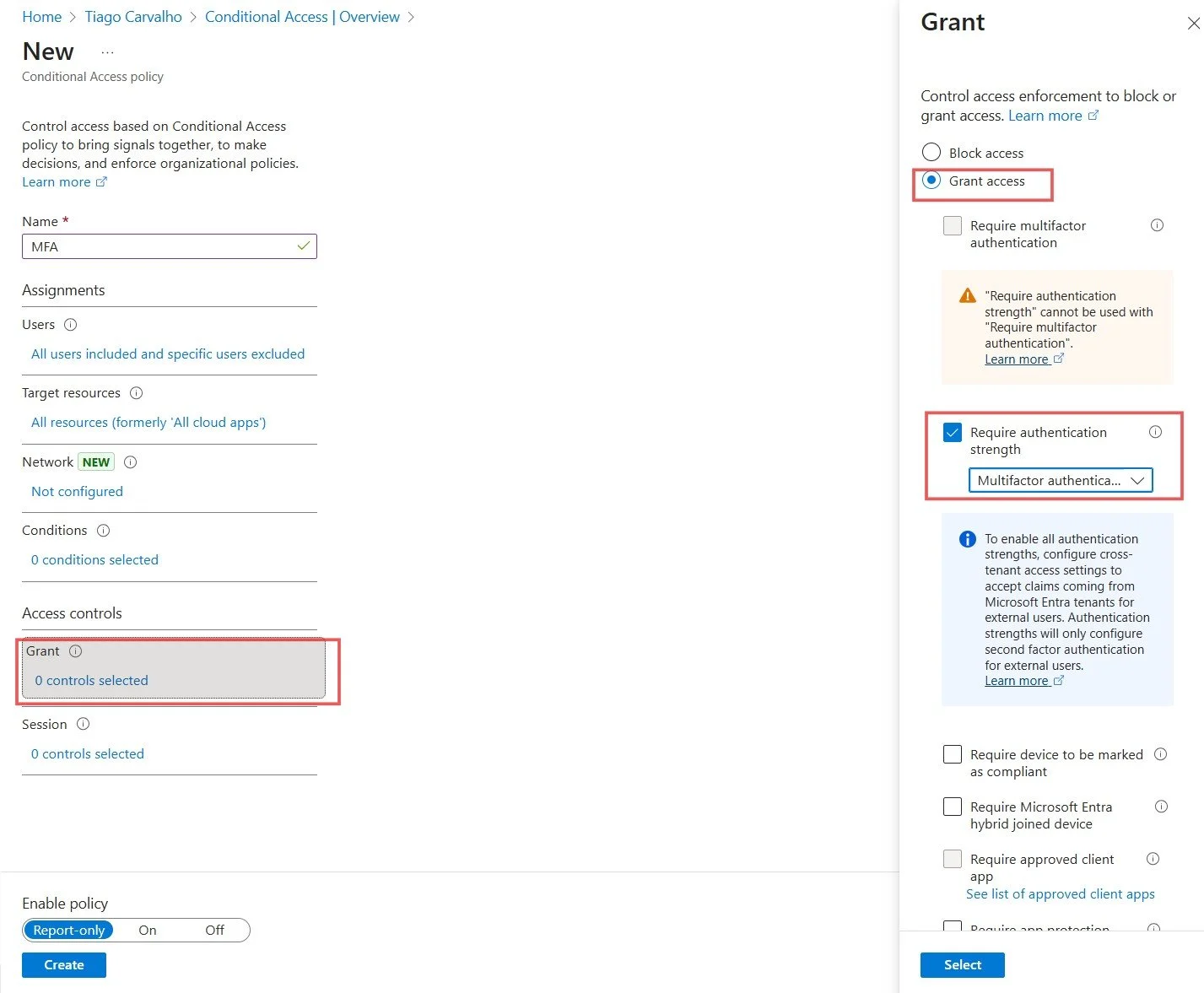
Step 5: Configure Access Controls - Grant
This is where you define the action. Click on Grant under Access controls. Select Grant access, and then check the box for Require authentication strength. From the dropdown, choose the built-in Multifactor authentication strength. This is Microsoft's recommended setting for a strong, baseline MFA requirement.
Figure 5: Requiring 'Multifactor authentication' strength as the grant control.
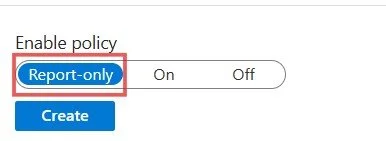
Step 6: Enable the Policy in Report-Only Mode
Before enforcing the policy, it is crucial to test its impact. At the bottom of the blade, under Enable policy, set the toggle to Report-only. This allows you to monitor the policy's effects in the sign-in logs without actually enforcing it on users. It provides a safe way to validate that the policy behaves as expected.
Figure 6: Setting the policy to 'Report-only' mode for safe testing.
Finally, click Create to save the policy.
Best Practices for Deployment
A successful deployment goes beyond just creating the policy. Follow these best practices to ensure a smooth and secure rollout.
1 Test with Report-Only Mode
Leave the policy in Report-only mode for several days. Analyze the sign-in logs in Microsoft Entra to see which users and apps would be affected. This helps you identify any potential issues, such as legacy applications or service accounts that might be impacted, before you enforce the policy.
2 Communicate with Users
Inform your users about the upcoming change. Provide them with clear instructions on how to register for MFA using the Microsoft Authenticator app. A well-planned communication strategy minimizes helpdesk calls and ensures a smoother user experience.
3 Phased Rollout
Instead of enabling the policy for "All users" at once, consider a phased rollout. Start with a pilot group of IT staff and tech-savvy users. Gradually expand the policy to different departments until the entire organization is covered. This approach allows you to address issues on a smaller scale.
4 Monitor and Refine
Once the policy is enforced, continue to monitor the sign-in logs and Conditional Access insights. Look for failed sign-ins and user feedback to identify areas for improvement. You may need to create additional, more granular policies for specific scenarios, such as excluding trusted corporate network locations.
Conclusion
Implementing a Conditional Access policy to require MFA for all users is the single most effective step you can take to secure your Microsoft 365 environment and begin your Zero Trust journey. It moves your security posture from being reactive to proactive, protecting your organization's identities and data before a compromise can occur.
By following this guide, you have built a powerful, enforceable, and compliant security control that aligns with modern best practices. This foundational policy not only drastically reduces your organization's attack surface but also paves the way for more advanced Zero Trust scenarios, such as device compliance, risk-based policies, and application protection. Welcome to the future of identity security.
References
- Weinert, A. (2020). Your Pa$$word doesn't matter. Microsoft Entra Identity Blog. https://techcommunity.microsoft.com/t5/microsoft-entra-azure-ad-blog/your-pa-word-doesn-t-matter/ba-p/1216821
- Microsoft. (2025). Plan a Conditional Access deployment. Microsoft Learn. https://learn.microsoft.com/en-us/entra/identity/conditional-access/plan-conditional-access
- Microsoft. (2025). What is Conditional Access in Microsoft Entra ID?. Microsoft Learn. https://learn.microsoft.com/en-us/entra/identity/conditional-access/overview