How to Implement Endpoint Privilege Management (EPM) in Microsoft Intune
In modern IT, achieving a Zero Trust security posture is paramount. One of the core principles of Zero Trust is least privilege access, which dictates that users should only have the permissions necessary to perform their jobs. For years, IT administrators have struggled with the challenge of removing local administrator rights from users without hindering their productivity. Users often need to perform tasks that require elevated privileges, such as installing software, updating drivers, or running legacy applications.
Endpoint Privilege Management (EPM), a component of the Microsoft Intune Suite, is the solution to this problem. EPM allows standard users to run specific, approved applications with elevated privileges, without ever granting them permanent administrator rights. This guide will walk you through the entire process of implementing EPM in your environment, from initial auditing to full enforcement.
Prerequisites
Before you begin, ensure you have the following:
- Licensing: Microsoft Intune Suite or a standalone EPM license.
- Permissions: You must be a Global Administrator or an Intune Administrator in Microsoft Entra ID.
- Platform: EPM is supported on Windows 10 and Windows 11 devices.
- Device Enrollment: Devices must be enrolled in Microsoft Intune.
The EPM Workflow
Understanding the EPM workflow is crucial for a successful implementation. The following diagram illustrates how EPM evaluates and handles elevation requests:
Step-by-Step Implementation Guide
Step 1: Enable EPM and Start Auditing (Phase 1)
The first step is to enable EPM on your devices and start collecting data. This is done by creating an Elevation Settings Policy. In this initial phase, you will not enforce any rules; you will simply audit what applications users are trying to elevate.
- Navigate to the Intune Admin Center:
Go toEndpoint security > Endpoint Privilege Management. - Create the Elevation Settings Policy:
- Click on the Policies tab.
- Click Create Policy.
- Select Windows 10 and later as the platform and Elevation settings policy as the profile.
- Give the policy a name, such as
EPM - Enable and Audit.
- Configure the Policy:
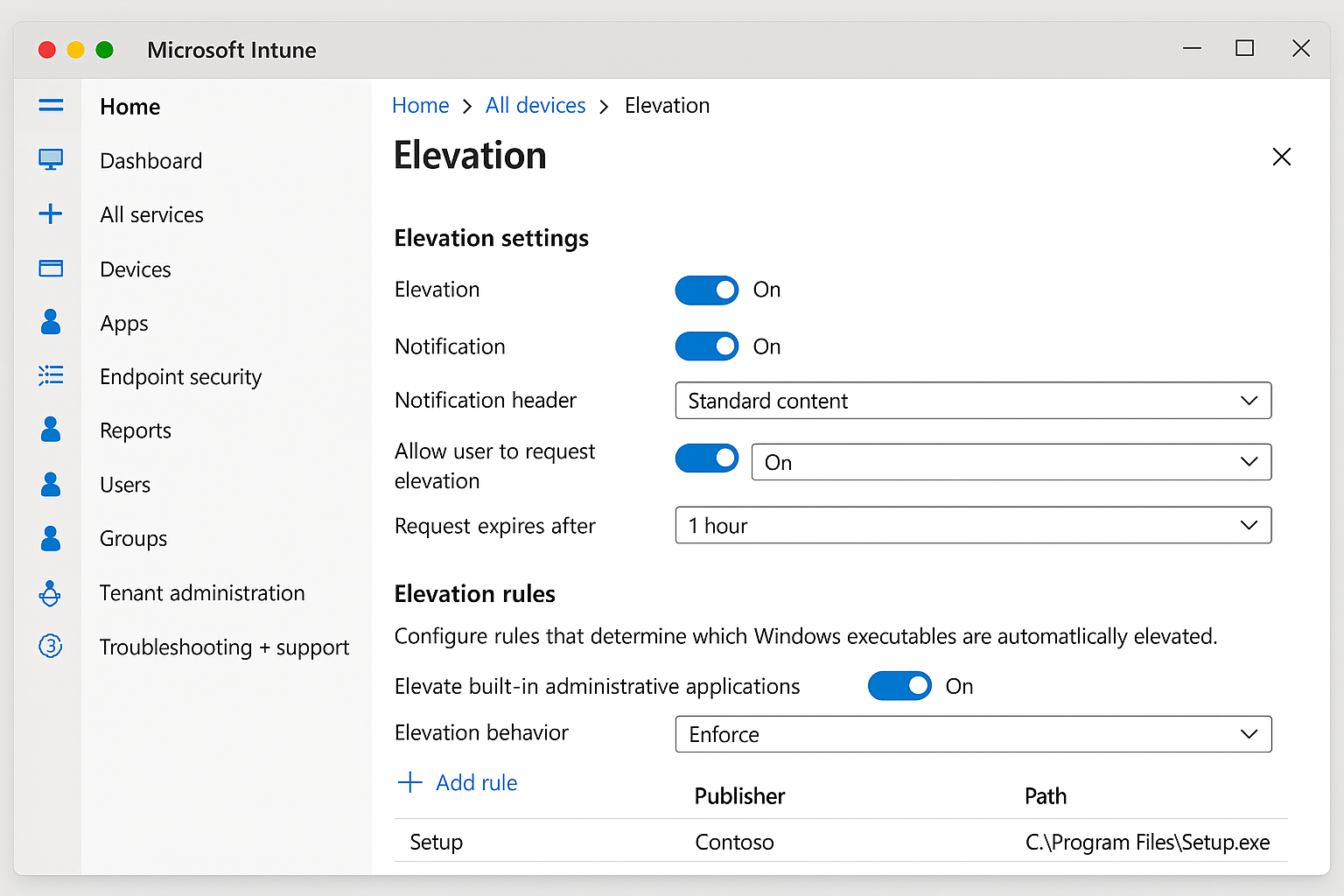
Configuring EPM Elevation Settings in the Intune Admin Center
- Endpoint Privilege Management: Set to Enabled.
- Default elevation response: Set to Deny all requests. This ensures that no elevations occur during the audit phase.
- Send elevation data for reporting: Set to Enabled. This is critical for collecting the data you will need to create rules.
- Validation criteria: Leave the default settings for now.
Assign the policy to a pilot group of users or devices. It is recommended to start with a small, representative group.
Step 2: Analyze Elevation Data (Phase 2)
After a few days of auditing, you will have collected valuable data on which applications your users are trying to elevate.
- Navigate to the EPM Reports:
Go toEndpoint security > Endpoint Privilege Management > Reports. - Review the Elevation Reports:
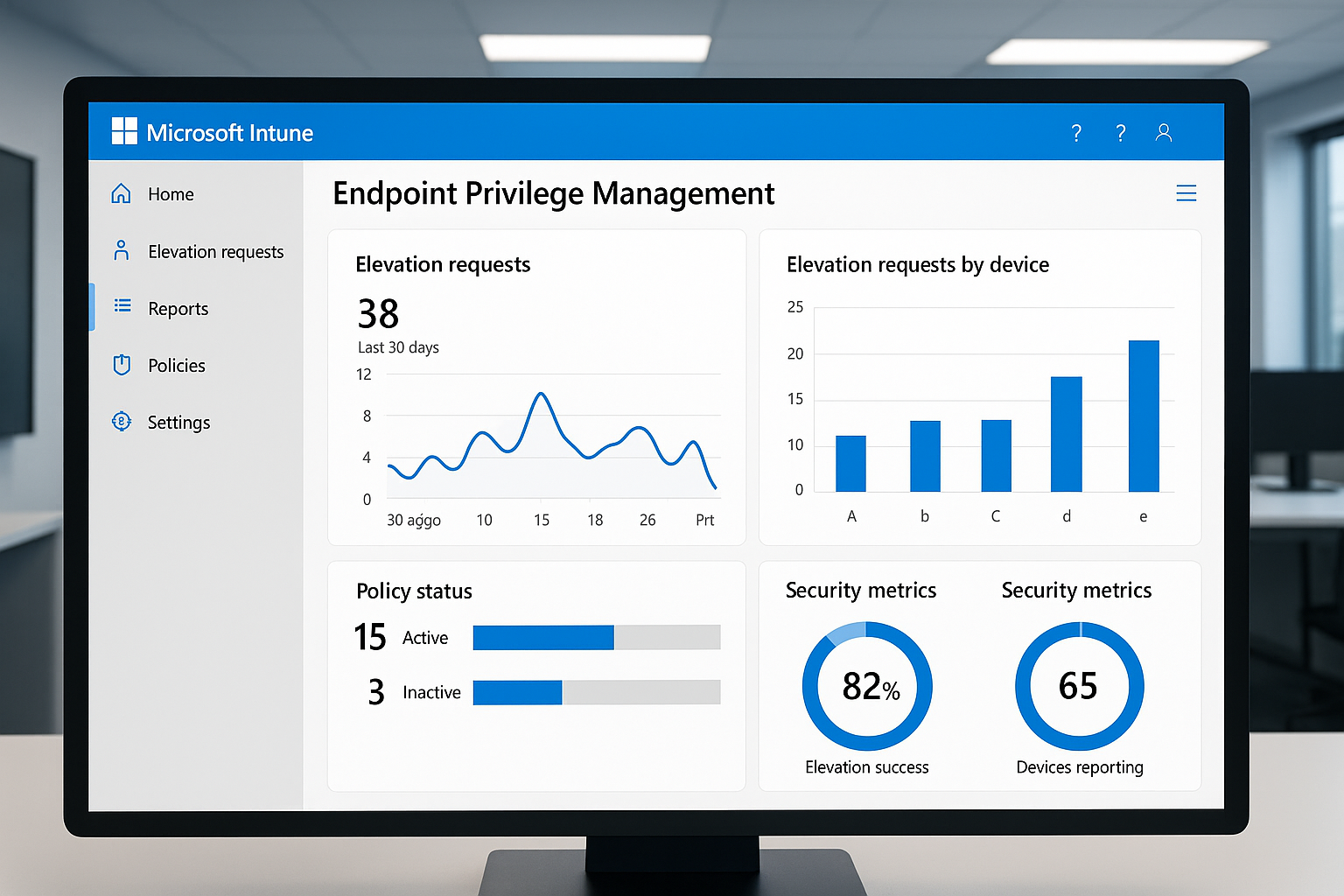
EPM Dashboard showing elevation requests, policy status, and security metrics
- The Endpoint Privilege Management elevation report will show you a list of all elevation requests.
- Analyze the data to identify common applications that require elevation. Look for patterns based on user roles or departments.
Step 3: Create Elevation Rules (Phase 3)
Now that you have identified the necessary applications, you can create Elevation Rules Policies to allow specific elevations.
- Create an Elevation Rules Policy:
- Go back to
Endpoint security > Endpoint Privilege Management > Policies. - Click Create Policy.
- Select Windows 10 and later as the platform and Elevation rules policy as the profile.
- Give the policy a name, such as
EPM - Application Elevation Rules.
- Go back to
- Define the Rules:
- Click Add to create a new rule.
- Rule name: Give the rule a descriptive name (e.g.,
Allow Notepad++ Installation). - Elevation type: Choose User confirmed. This is the recommended starting point, as it requires the user to provide a justification for the elevation.
- File information: You can define the file by:
- File path: The full path to the executable.
- File hash: The SHA256 hash of the file (most secure).
- Certificate: The signing certificate of the application.
Example Rule for Notepad++:
- File name:
npp.8.6.installer.x64.exe - File hash:
(Get the hash from the EPM report or by using PowerShell)
- Assign the Policy:
Assign this policy to the same pilot group.
Step 4: Monitor and Refine (Phase 4)
Continuously monitor the EPM reports to see how your rules are working. You may need to refine your rules or create new ones as you discover new scenarios. Over time, you can move from User confirmed to Automatic elevation for trusted applications.
Step 5: Remove Local Admin Rights (Phase 5)
Once you are confident that your EPM rules cover the majority of your users' needs, you can begin the process of removing local administrator rights.
- Create a Local User Group Membership Policy:
- Go to
Endpoint security > Account protection. - Click Create Policy.
- Select Windows 10 and later as the platform and Local user group membership as the profile.
- Go to
- Configure the Policy:
- Local group: Select Administrators.
- Group and user action: Select Remove (Update).
- User selection type: Select Users.
- Selected users/groups: Add the users or groups from whom you want to remove admin rights.
- Assign the Policy:
Assign this policy to your pilot group.
Best Practices and Troubleshooting
- Start with a Pilot: Always test EPM with a small group of users before deploying it to your entire organization.
- Communicate with Users: Inform your users about the changes and provide them with training on the new EPM process.
- Use File Hashes: Whenever possible, use file hashes for your elevation rules. This is the most secure method.
- Enable Support-Approved Elevation: For edge cases that are not covered by your rules, consider enabling support-approved elevation. This allows users to request an elevation that can be approved by an administrator in the Intune portal.
- Review Reports Regularly: The EPM reports are your best friend. Use them to monitor the effectiveness of your policies and identify any issues.
Conclusion
Implementing Endpoint Privilege Management is a critical step towards a Zero Trust security model. By removing local administrator rights and providing a controlled way for users to elevate applications, you can significantly reduce your organization's attack surface without sacrificing user productivity. By following this guide, you can successfully deploy EPM in your environment and take a major step forward in your security journey.